Most employees are working from home due to the COVID-19 situation. Therefore, organizations have the challenge if they permit using none company-owned workplaces. This blog describes my common practices about how you can secure Cloud applications from unmanaged devices via Conditional Access policies. For now, I use Microsoft Teams combined with the protection of Conditional Access as an example.
The idea for this blog started with a simple question about the choices an organization had to use Microsoft Teams from none company-owned workplaces. Usually, I encourage organizations to only using corporate resources from managed (mobile)-workplaces. The employees can no longer visit the office buildings to have access to their systems. Besides, that organizations can not invest in a large number of mobile workplaces because the stock by retails is deficient and not include the year budget. Due to the situation, employees use their personally owned workplaces temporally to be able to work from home.
Use Conditional Access
Anytime a user authenticates to Microsoft Teams, Azure Active Directory handles the authentication request. It’s likely that you heard of Azure Active Directory Conditional Access but do not understand all the capabilities. No problem I explain it from both a functional and technical point of view.
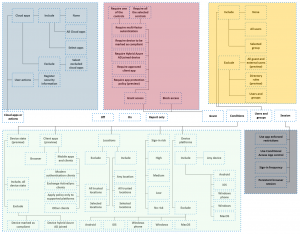
The layout left is a schematic overview of all the components of the conditional access policy (June 2020). A person with a technical background can figure-out easily how to compile a policy to archive the organization’s goals (see this blog).
Building the Bridge
However, can you use the same diagram for a CISO? I have experienced this is not possible. You need to build a bridge between the technical capabilities and real-life scenarios. Let’s start with the example of Teams where the CISO has indicated all the minimum (security) requirements for accessing the application.
- The Microsoft Teams application is accessible from compliant workplaces without user interactions like MFA.
- The organization’s data can only be saved locally when the device is managed and marked as compliant.
- The mobile application protects the data via application management policies to containerize the organization’s (sensitive) data. Therefore it avoids copying data to uncontrolled locations.
- The web application is accessible from any none compliant device with an MFA challenge.
Hello, SecOps engineer. Now it’s your turn! How do you protect the company resources like Microsoft Team while anyone works from home? [answer engineer ] We use enforced MFA. Great because it stops the most common attacks. The employee’s productivity drops because they need to perform MFA-challenges multiple times per day. SecOps engineers want to increase their security posture while the employees are productive.
True story
Sounds this familiar to you?
Using a Functional Baseline
It’s not a simple task for engineers to define a conditional access baseline that contains as well the functional and technical requirements. And which option do I have to configure a Conditional Access policy?
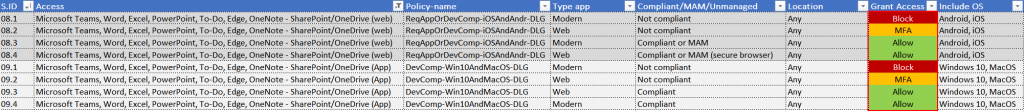
I have built an overview of a conditional access baseline that is explained in the above scenarios. If you select column B and filter on the product Microsoft Teams, you can see that my recommendations of allowing access with or without MFA or blocking an authentication require in a specific scenario.
Summary
Building a robust conditional access baseline for a Cloud application is difficult if you only explain it from a technical aspect. Therefore, you need to translate functional requirements to technical capabilities. To give you a fabulous start, I share my best practices for (Cloud) applications like but not limited to Microsoft Teams only.
Related blogs
- Why do I need a second authentication factor? – WorkplaceAsCode.com
- Insights in privilege accounts via workbooks – WorkplaceAsCode.com
- A robust Conditional Access baseline sample – WorkplaceAsCode.com

I have been involved in Tristains Workshop and Awesome!!!!!!!